Web Application Penetration Testing – In this digital era, every business needs to have a strong web presence. This is much more significant for businesses that rely on internet sales and transactions. However, with so many websites springing up, distinguishing oneself from the competition might be difficult. This is when online application penetration testing comes in handy. By identifying and resolving vulnerabilities in your web application, you can improve your website’s security and give yourself a competitive edge. We’ll go through what a web application is, how it works, and why you should conduct penetration testing in it, in this blog post. We will also take a look at some of the most popular tools used for this type of testing.
Table of Contents
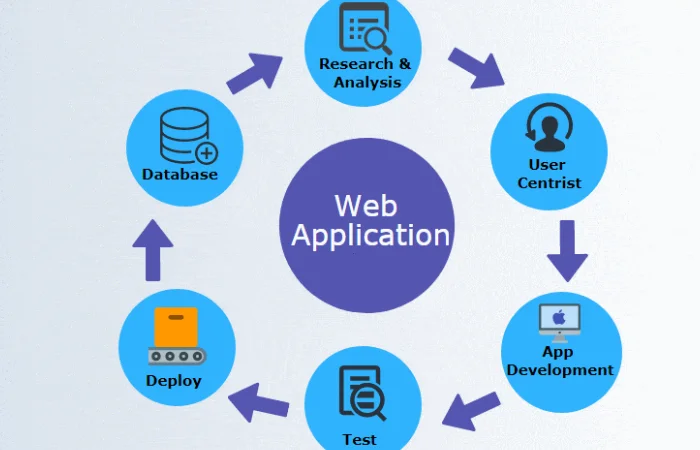
What Are Web Applications?
A web application is a software program that is accessed over the internet. A website can range from a simple static page to an e-commerce site with a checkout process. Web applications must be hosted on a web server to be accessible over the internet.
What Is Web Application Penetration Testing?
Web application penetration testing, sometimes called web application security auditing or web application vulnerability testing, is the practice of finding and exploiting flaws in a website. By doing this, penetration testers can gain access to sensitive data, bypass security controls, and even take control of the entire system.
Why Is Web Application Penetration Testing Necessary?
There are several motives for performing a web application pentest. The most common reason is to find and fix any security vulnerabilities that can be exploited by hackers. By detecting and correcting these flaws, you can decrease the likelihood of your website being hacked. Penetration testing can also be used to test the security of an application to meet regulatory compliance requirements.
What Are the Elements of Web Application Penetration Testing?
Web application penetration testing, as the name suggests, focuses on web applications. The following are some of the primary characteristics that distinguish web application penetration testing from other types of penetration testing:
- The ability to test a wide range of applications, including custom applications and websites
- The ability to identify and exploit vulnerabilities in a short amount of time
- The use of automated tools to quickly scan for vulnerabilities
- A focus on business-critical applications and systems
Steps For Web Application Penetration Testing
The following are the four basic phases of web application penetration testing:
- Reconnaissance- This is the first stage in our approach, which entails gathering information about the target system. This can be done through public sources or by conducting active scans.
- Scanning- The next step is to scan the target system for vulnerabilities. This may be accomplished with automated tools or manual testing.
- Exploitation- Vulnerabilities are discovered at this stage, and they may then be used to gain access to the system.
- Post-Exploitation- The final step is to escalate the privileges through the exploits to discover how damaging a certain vulnerability can be.
11 Popular Tools For Web Application Penetration Testing With Details
As a website or web application owner, it is your responsibility to ensure the safety and security of your site. Conducting regular penetration tests is one approach to accomplish this. Here are 11 of the most popular web application testing tools:
- Astra’s Pentest: A reliable pentesting tool provided by Astra’s Security with a wide array of features.
- Burp Suite: a toolkit for web application security testing that includes a proxy server, scanner, and intruder
- Netsparker: a vulnerability scanner that can identify over 25,000 different types of vulnerabilities
- OWASP ZAP: A free web application security scanner is available to the public.
- SQLMap: a tool for SQL injection exploitation
- AppScan: a web application security scanner from IBM
- Arachni: an open-source web application security scanner
- BeEF: a browser exploitation framework that can use to attack web applications
- wmap: a Web Application Attack and Audit Proxy
- WebGoat: A deliberately vulnerable web application that is use for training and testing.
- Wappalyzer: comes with a user-friendly interface, which allows security analysts to use it on their own without prior programming knowledge. It’s also cost-effective and has no licensing costs. It is based on the WapScan open-source penetration testing toolkit.
These are just a few of the many different tools that are available for web application penetration testing. And the ideal approach to locate the appropriate tool for your needs is to engage a professional penetration tester. Also, They’ll be able to examine your unique demands and recommend the most effective tools for you. And if you want to make your website more secure also, you’ll need to have a penetration test done on it.
Conclusion
As a web application owner, it is important to know that your site is not only being access by legitimate users but also by malicious actors who are looking for vulnerability.
Also penetration testing can help identify these vulnerability and help you fix them before they can exploite. While there are many different penetration testing methodologies, following the steps we’ve outlined should give you a good foundation for starting out.
Author Bio-
Ankit Pahuja is the Marketing Lead & Evangelist at Astra Security. Ever since his adulthood (literally, he was 20 years old), he began finding vulnerabilities in websites & network infrastructures. And starting his professional career as a software engineer. Also at one of the unicorns enables him in bringing “engineering in marketing” to reality. Working actively in the cybersecurity space for more than 2 years makes him the perfect T-shaped marketing professional. Ankit is an avid speaker in the security space and has delivered various talks in top companies also, early-age startups, and online events.

Also Read: Introducing B2Broker’s New White Label cTrader Platform

